The main intention with which people seem to make more and more use of computer forensic investigators is to either detect and secure or retrieve relevant information an organization or institution needs, for the purpose of stating and rendering firm conclusions.
 The generally assumed field that became a top of mind is the delinquency area, although the original meaning of the computer forensic field term was used to describe civil procedures. The principles involved are mostly similar to the data recovery course to which the know-how also requires a legal audit trail, which is a chronogical record also security – relevant, providing documented proof of the sequence of given activities that altered specific procedures or processes. While the range of using such evidence in court is more widely spread, both the european and American cultures begin to develop legal frameworks to factually accept it in an official manner.
The generally assumed field that became a top of mind is the delinquency area, although the original meaning of the computer forensic field term was used to describe civil procedures. The principles involved are mostly similar to the data recovery course to which the know-how also requires a legal audit trail, which is a chronogical record also security – relevant, providing documented proof of the sequence of given activities that altered specific procedures or processes. While the range of using such evidence in court is more widely spread, both the european and American cultures begin to develop legal frameworks to factually accept it in an official manner.
The discipline, as well as the practice, surprises the legal framework of the state in question by which specific technological processes are admissible in front of a court in order to prove guilt or innocence in cases of rights violations or protocol infringement. These include data services, data transfer, wireless communications involving specific information such as the spectrums of illegal usage of intellectual property or children pornography. Also, if the information an organization beholds of a client fails to be protected according to the signed agreement and the law of Parties, the consequences make it liable in either civil or criminal court.
The process is truly belaboured and it involves advanced knowledge in both Laws and computer science, as it was previously mentioned. Withal, the tools and techniques required for any specific investigation procedure depend on the nature of the case to be solved as well as to the purpose of the investigations. There are two main types of data that the investigators in computer forensics collect. The first one is persistent data, consisting of information stored on a local hard drive, stored while the device is turned off, while the volatile data is going to be lost when the device is turned off, the information being either stored in the memory or in transmitting process. This second type of data remained in the registers and the random access memory (RAM) and can be accessed after the operation has ended, if the instruments used are properly chosen.

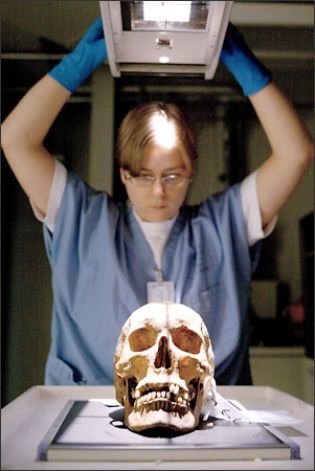
Similarly to any other type of research, the forensic investigations imply specific stept to be followed. Identifying the purpose and the nature of the investigation and the tools needed for the entire procedure to take place is only the first stage of the reasearch, while the second one consists in the evidence acquisition, i.e. the identification of the sources of digital evidence to pe preserved.
During the third stage the investigator decides what are the best tools to be used in the specific procedure, performs the data process and renders the interpretation of the analysis results. Finally, the obtained results are disseminated in reported findings and presented findings. The most important two goals that have to be accomplished for the computer forensic investigation to be successful are to be practiced effectively, under legal conditions and to draft the basic theoretical information that lends itself to be used.